Cybersecurity Services
Elinext: Leading Experts in Compliance Consulting Solutions
Elinext offers expert compliance consulting solutions to help businesses meet industry standards and avoid risks. With years of experience across regulated sectors, we make your processes align with GDPR, HIPAA, ISO, and more.
Elinext offers expert compliance consulting solutions to help businesses meet industry standards and avoid risks. With years of experience across regulated sectors, we make your processes align with GDPR, HIPAA, ISO, and more.
Cybersecurity Services We Offer
-
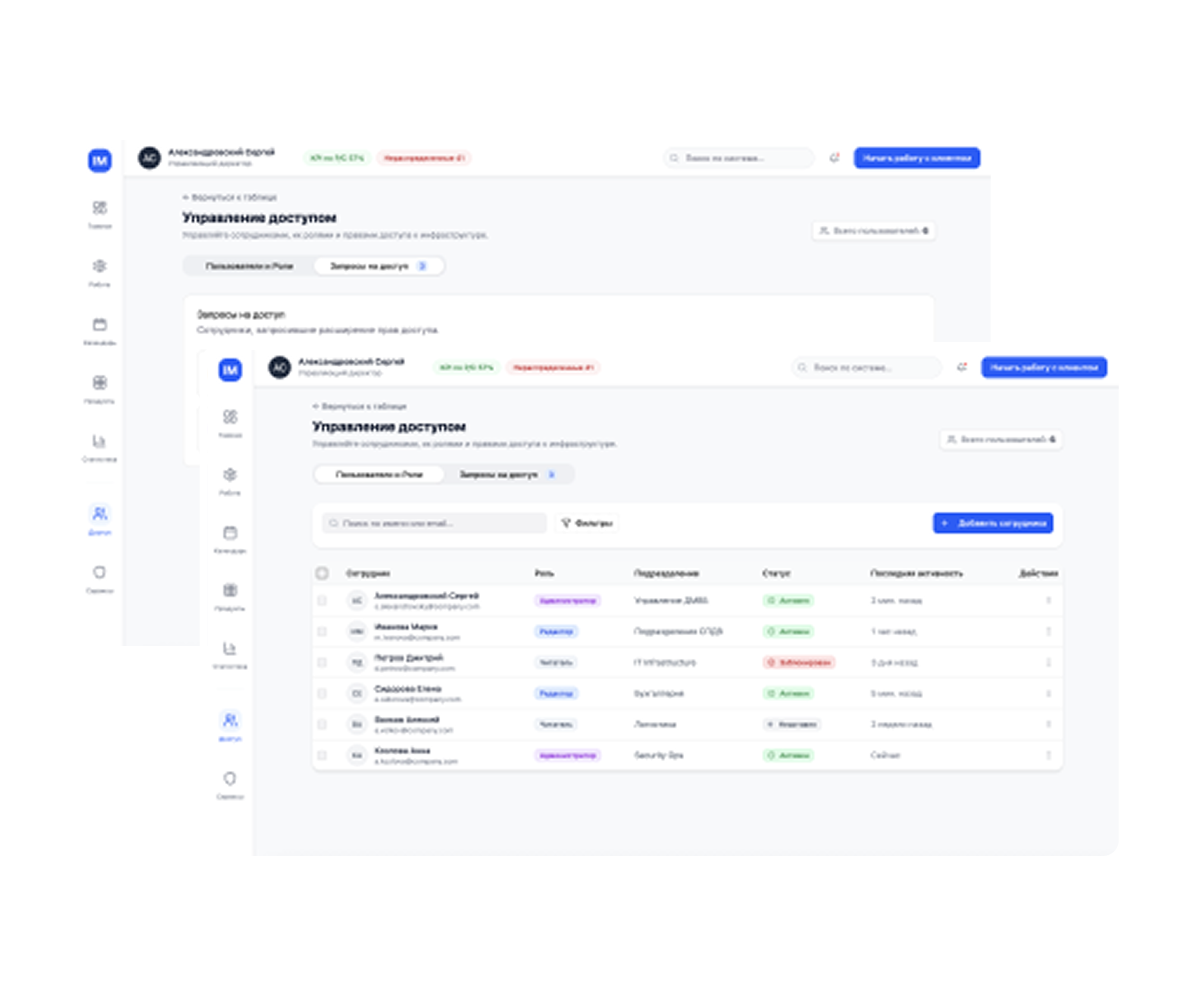
Cloud Security Services
Cloud security includes policies, controls, and technologies that protect cloud systems, data, and infrastructure. Elinext supports key areas of cybersecurity services, from access authentication to traffic filtering.
-
Endpoint Security Services
Endpoints are vulnerable access points to your network. Elinext secures them by enforcing compliance with data protection standards as part of our cybersecurity services, reducing the risk of breaches and unauthorized access.
-
Network Security Services
Every organization needs network security to defend against growing cyber threats. Elinext delivers rules and tools – both hardware and software – to protect your data and systems’ integrity, confidentiality, and availability.
-
Application Security Services
We secure your applications across the development lifecycle with code analysis, vulnerability testing, and cybersecurity services best practices to prevent cyber threats.
-
SIEM Services
Elinext implements and manages SIEM systems for real-time threat detection, incident response, and log management, ensuring full visibility across environments.
-
Data Protection Services
We provide encryption, access control, and backup solutions within our cybersecurity services, safeguarding sensitive data and helping meet GDPR, HIPAA, and other regulatory requirements.
-
Risk Management Services
Our experts assess, prioritize, and mitigate IT security risks through strategic cybersecurity services, including planning, compliance alignment, and proactive vulnerability management.
-
DevSecOps Implementation
Elinext integrates security into DevOps pipelines by applying cybersecurity services, enabling fast yet secure deployments with automated scanning, policy enforcement, and compliance checks.
-
Managed Security Services
We offer 24/7 monitoring, threat detection, and response through our managed services, reducing risk while freeing your team to focus on core business.
Our Awards and Recognitions
Cybersecurity
Consulting Services by Elinext
What Our Experts SayWhat Our Experts Say



Cybersecurity Testing Services
by Elinext
-
Vulnerability Assessment Services
We identify and analyze weaknesses in your systems, networks, and apps, prioritizing risks and helping you take action before threats can be exploited.
-
Security Assessment Services
Elinext performs thorough evaluations of your infrastructure, policies, and defenses to measure resilience against current and emerging cyber threats.
-
Compliance Assessment Services
We help ensure your organization meets regulatory requirements like GDPR, HIPAA, or ISO standards, reducing the risk of non-compliance penalties and breaches.
-
Penetration Testing Services
Our ethical hackers simulate real-world attacks to test your defenses, uncover security gaps, and provide actionable recommendations to fix vulnerabilities.
-
Security Code Review Services
We analyze your application’s source code to detect security flaws, logic errors, and compliance gaps, secure and clean development practices.
-
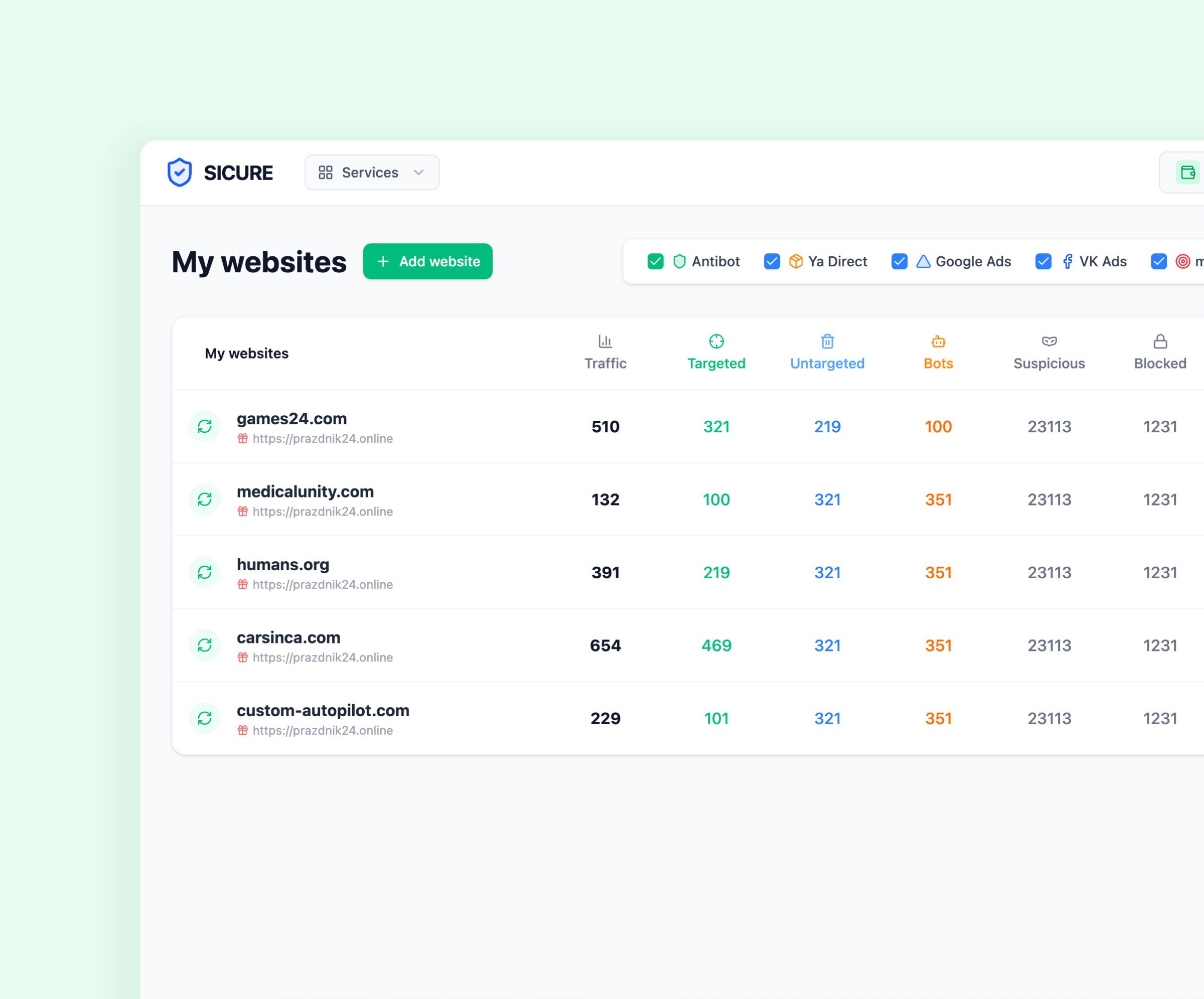
DDoS Testing Services
We simulate distributed denial-of-service attacks to evaluate your system’s resilience, helping you prepare for and mitigate real DDoS threats effectively.

Our Cybersecurity Services for
IT Components
Elinext secures your entire IT ecosystem - from infrastructure to applications, ensuring end-to-end protection against modern and evolving cyber threats.
-
On-premises Infrastructures
We protect local servers, storage, and networks with customized firewalls, access controls, and regular audits to prevent unauthorized access and breaches.
-
Cloud Environments
We secure multi-cloud and hybrid environments through identity management, encryption, and compliance-ready architectures tailored to each platform.
-
External and Internal Networks
We monitor and secure both external and internal traffic, detecting threats, preventing breaches, and ensuring safe, segmented network communication.
-
Databases
We protect databases against injection attacks, unauthorized access, and data leaks through encryption, role-based access, and real-time monitoring.
-
Web and Mobile Applications
Elinext performs in-depth security testing and implements app-level protections to block threats like XSS, CSRF, and insecure data storage.
-
Websites and Web Portals
We secure websites and portals with SSL/TLS, WAFs, DDoS protection, and code audits, guarding against intrusion and ensuring data privacy.
-
APIs and Microservices
Our team protects APIs and microservices by enforcing authentication, rate limiting, and encryption, securing data flows across distributed systems.
-
Development Infrastructures
We secure CI/CD pipelines, source code repositories, and dev environments to prevent supply chain attacks and maintain code integrity.
-
Email Services
We help secure your email systems with spam filters, phishing detection, and encryption, reducing the risk of fraud and data compromise.
-
IoT Devices and Infrastructures
We safeguard IoT ecosystems by securing firmware, managing device identities, and isolating vulnerable endpoints from critical infrastructure.
-
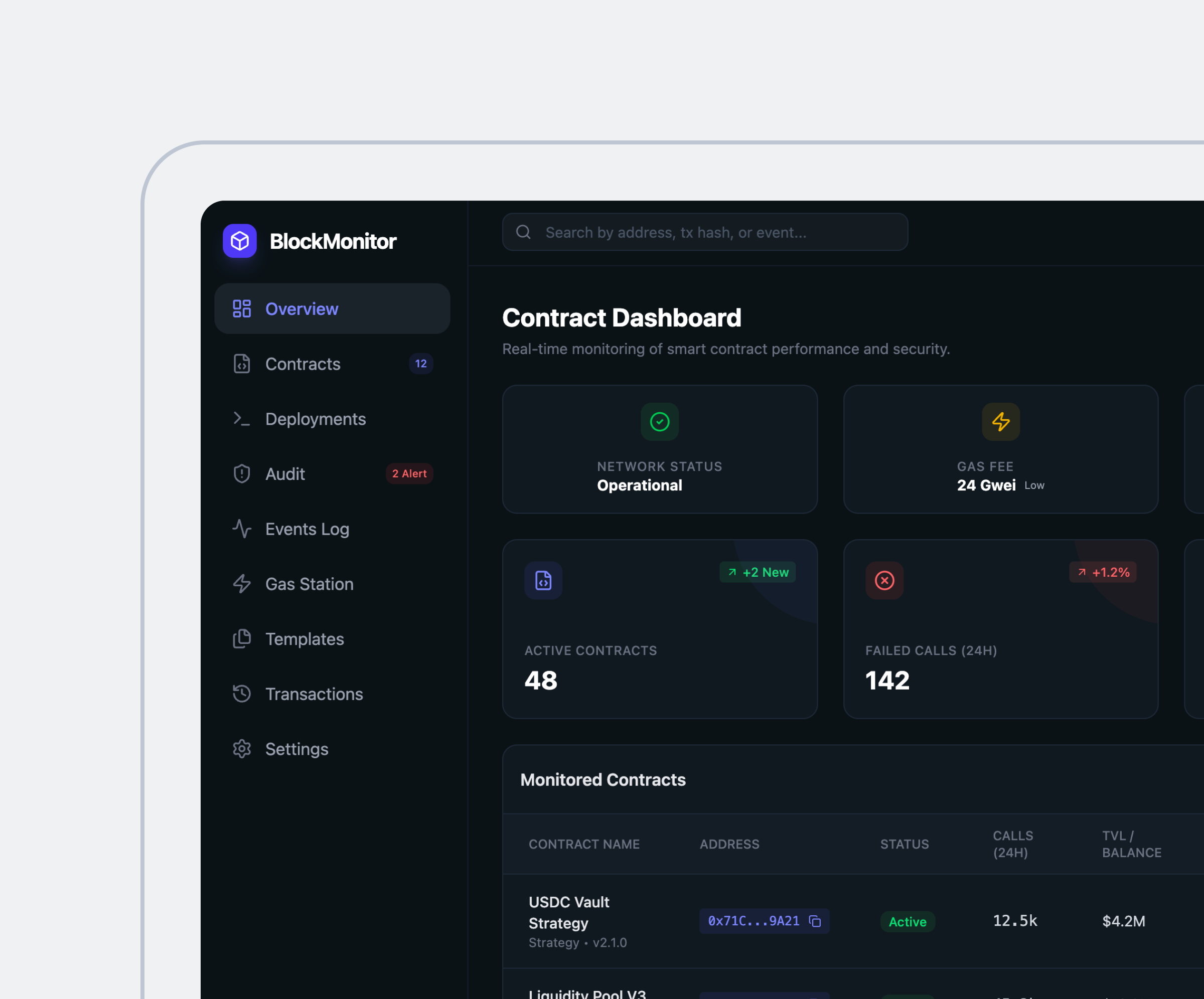
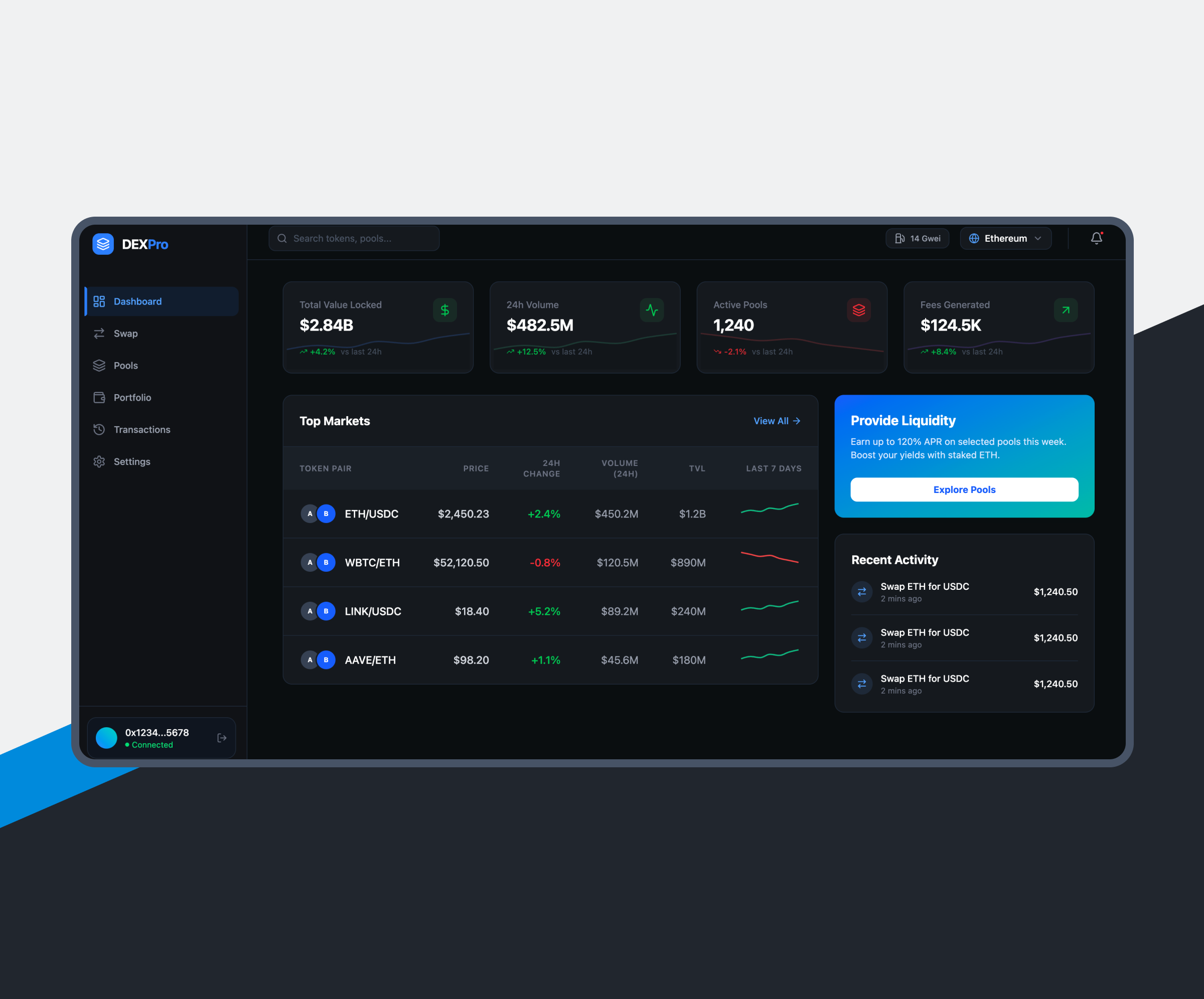
Blockchain Networks
Elinext ensures the integrity and security of blockchain nodes, consensus mechanisms, and data flows through rigorous audits and monitoring.
-
Smart Contracts
Our experts perform security audits on smart contracts to detect flaws and prevent exploits, ensuring trustworthy, tamper-proof blockchain transactions.
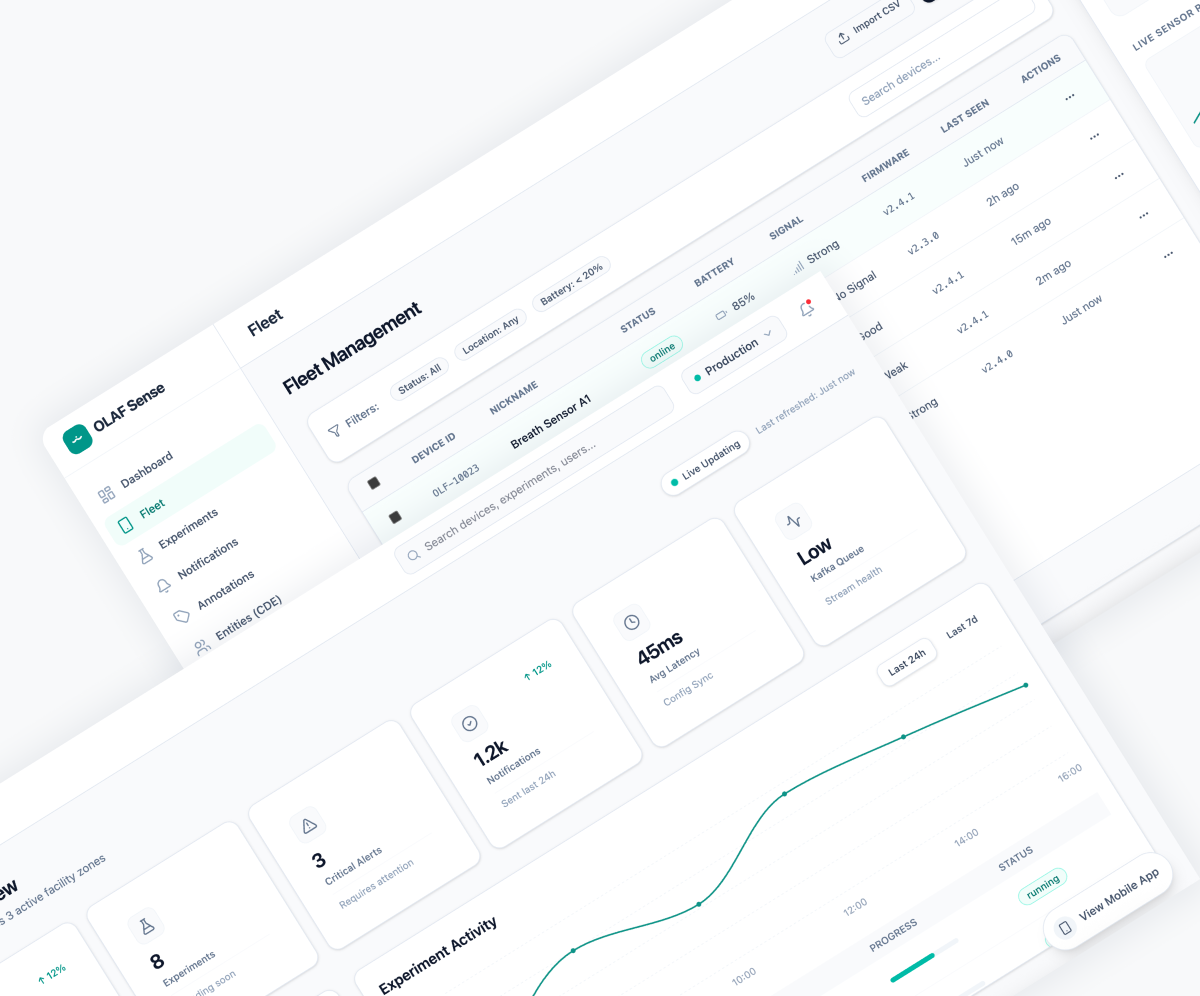
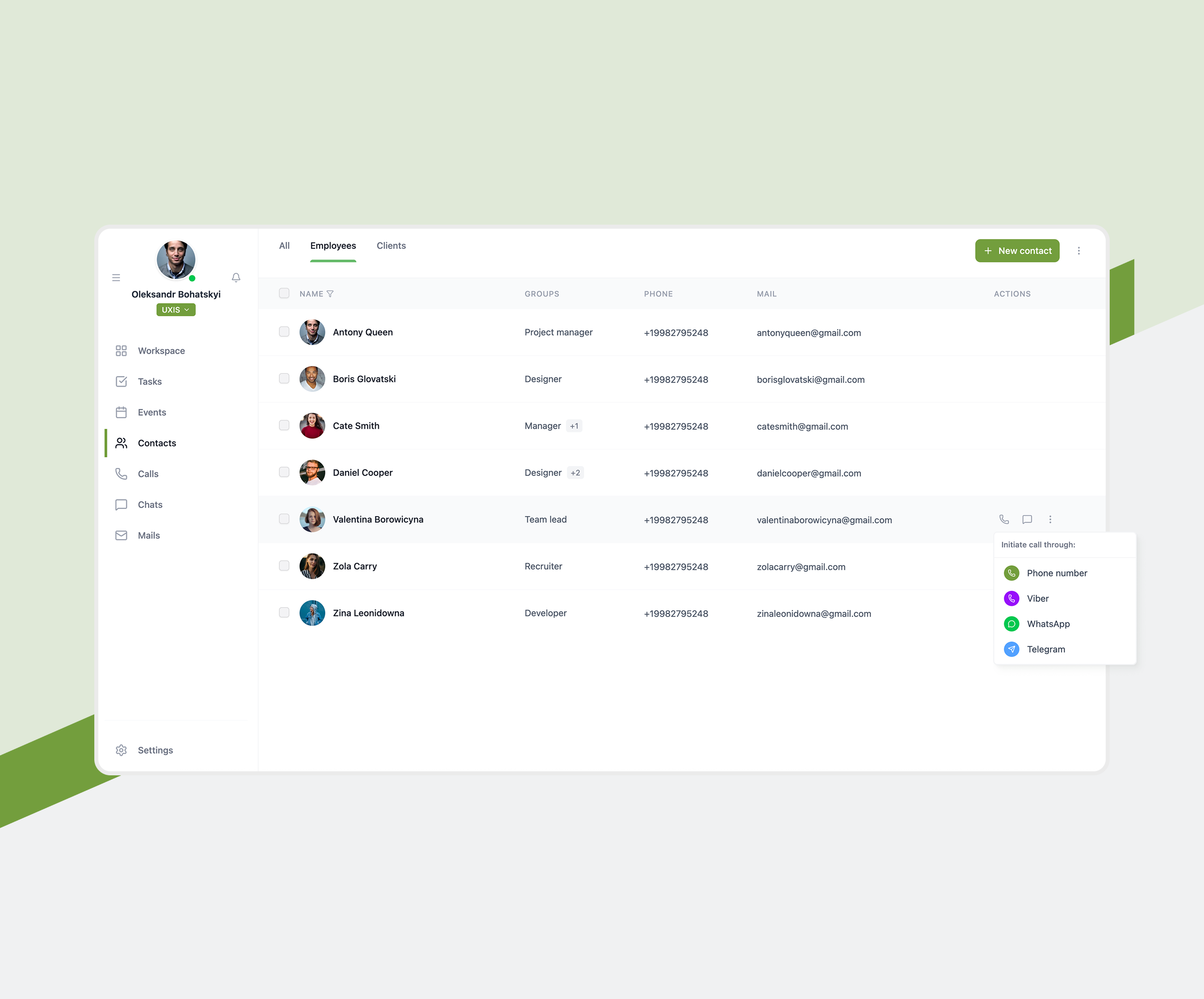
AI-Powered
Cybersecurity Compliance Software
…
Industries We Serve
The Benefits of
Cybersecurity Solutions by Elinext

Choose Your Service Option
Leverage cybersecurity expertise
Hire dedicated cybersecurity engineers
Let us handle your cybersecurity services project
Hire Cybersecurity Engineers
from Elinext
Why Elinext?
Listen to Our Clients
FAQ
-
They protect your digital assets through cybersecurity services such as risk assessment, threat detection, prevention, and response to cyber attacks, ensuring data privacy and system integrity.
-
To safeguard sensitive data, comply with regulations, prevent costly breaches through professional cybersecurity services, and maintain customer trust in an increasingly digital world.
-
We analyze your infrastructure, identify vulnerabilities, review policies, and evaluate risks using structured cybersecurity services to tailor a security strategy that fits your business goals.
-
At least annually, or whenever major changes occur in technology, regulations, or threat landscapes, to ensure ongoing protection through updated cybersecurity services and compliance.