Project Background
Elinext was contacted by a German customer headquartered in Munich who was interested in the development of a messenger with the highest levels of security and encryption possible.
Requirements
What our customer needed, was some sort of app that would provide a protected untraceable connection channel. Basically, it was a task for a top-secret messenger with an unprecedented level of encryption and security.
During the development process, the requirements were widened, and in addition to the app, the whole special operational system was ought to be developed for providing the advanced level of data security.
Challenges
The main task was to develop the device equipped with an operating system that wouldn’t allow the user to “shoot himself in the leg” by creating openings for information leaks. That is why a device running on.
There were plenty of requirements for the Android-based operational system developed specifically for our client:
- Сalls are disabled, only outputs available are mobile Internet and Wi-Fi.
- The USB connection is prohibited
- No file system
- Prohibition for the system configuration
- Encrypted data storage
- Remote data management
- Absence of any apps besides the gallery and the chat
Development Process
The process of the development came in over 40 interactions. After we’ve defined the technologies and found the best options for OS customization our developers made a basic operating version of the product which was the starting point of the development.
The development of the messenger’s chat and OS modification were held parallelly.
Each iteration resulted in a ready product with a feature(s) realization. Some of these features were altered further in the process of development.
Solutions and Features
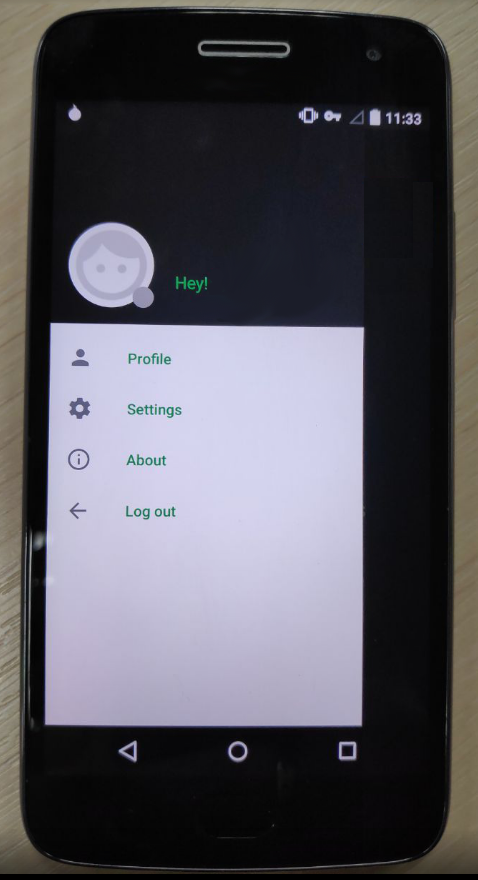
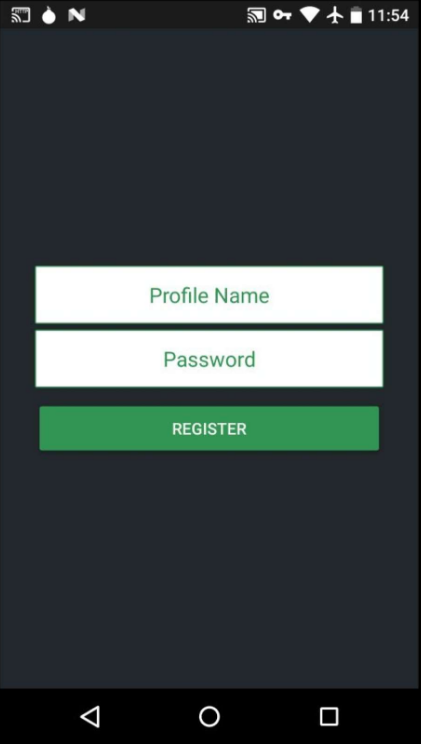
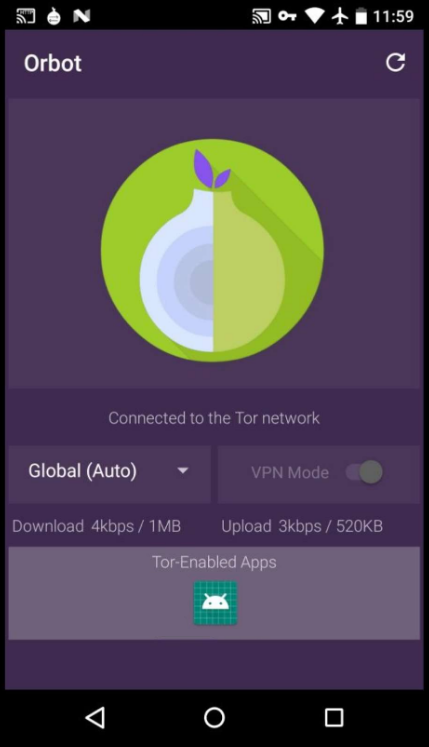
The final solution came as firmware for an Android phone. This is a ready product. Such firmware includes a modifier Android-based OS with pre-installed Messenger.
Two different developers worked on the messenger and the operational system and synched up their efforts to deliver the following features:
Messenger:
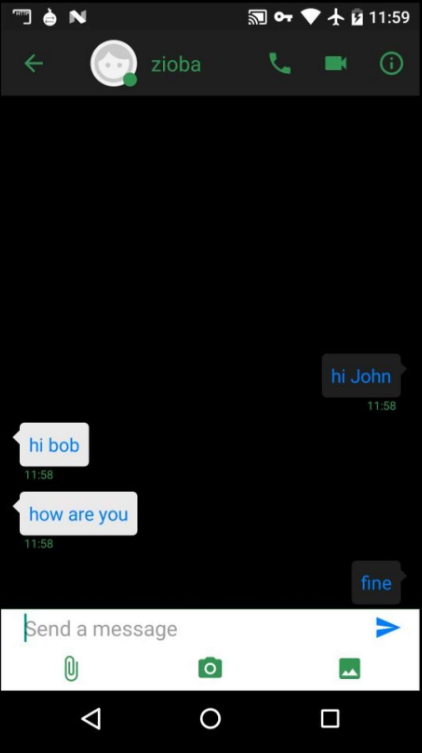
- Sending/receiving end-to-end encrypted messages
- Working with photos encryption of messages and files on storage
- Immediate storage wipe
- Design features
- Remote device wipe
- Remote device block/unblock
OS:
- Bluetooth, USB connection, logging, radio removal
- The full and complete cut of phone communication module (except for Internet)
- Curring of the front camera
- Implemented password to wipe the device
- Prohibition for apps installation
- Removal of numerous other functional settings in the phone
- Logos of device modification
- Removal of potentially security-threatening system apps.
Results
The Elinext software engineers completed the task of developing the messenger with the highest levels of security and data encryption. Also, in the process of development, Android OS was heavily customized towards creating a maximally secure solution.
The scope of work made for this project allows our development team to claim that they’ve gained additional expertise in working on embedded technology based on Android.
This shows Elinext’s expertise and the ability to create highly secure messengers using top levels of encryption.
Also, the startups feeding their customers with pre-installed custom firmware now can be sure they are able to rely on Elinext as a competent developer of such kind.
With this case, we prove that any necessary modification of an operating system for implementing the necessary features at the system level is no problem for our developers.
Some of the templates of similar development might also be used for smart home solutions.