Every website or company that accepts online payments in a certain form, must meet and follow the requirements of Payment Card Industry Data Security Standards (PCI-DSS). The standards are governed and established by major credit card companies (Visa, MasterCard, American Express, JCB and Discover).
The goal of being compliant with PCI-DSS is in ensuring the secure trans ition of monetary means and storing (handling) cardholder sensitive data.
We, as a software development company, like to tell you how we deal with requests of our clients on creating websites and software that deals with payments online.
Note: pay attention that this blog post is not, in any case, should be considered as legal advice. We are describing our experience only.
Anyhow, customers of your e-commerce company rely on your ability to protect their data. In most cases, this is vital for their protection, hence your stable operating.
We prepared this guide to explain the goals and requirements of PCI compliance, best practices for securing e-commerce websites, and tactics to combat threats against online stores.
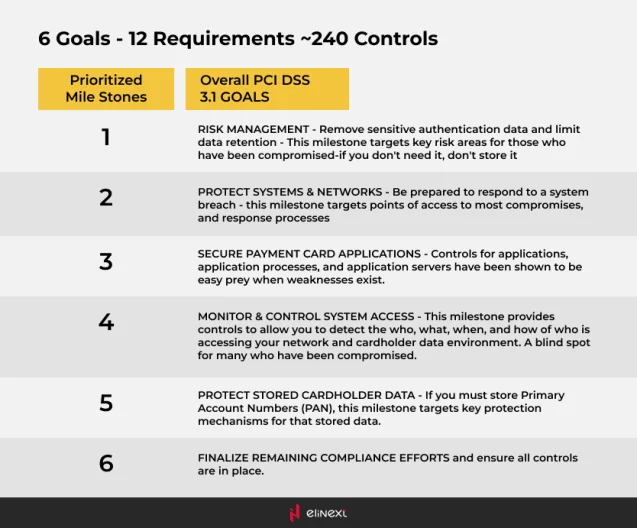
What is PCI Compliance?
The PCI Data Security Standards (PCI DSS) includes general practices, such as restricting cardholder information and the need for creating safe, non-default passwords, as well as more in-depth practices like encryption and the use of a firewall.
The PCI Security Standards Council is a global organization formed by major credit card companies, including Visa, Mastercard, Discover, and American Express.
If you operate an e-commerce site, PCI compliance is mandatory. It is not dictated by the volume of transactions or restricted solely to the storage, transmission, and processing; it applies to any business that allows credit card payments.
With PCI, everything is about reducing the attack surface. For an e-commerce site, this specifically involves the Card Data Environment (CDE) – the manner in which you handle credit cards on your site. Even if you leverage third-party services like Stripe, Recurly, PayPal, or another secure payment option, you have an obligation to follow the requirements as set forth by PCI DSS.
Small merchants are not excluded from these requirements. Unprotected e-commerce websites are prime targets for data thieves.
If sensitive customer data or cardholder information is stolen from a website that you’re responsible for, you could incur penalties, large fines, and even lose the ability to accept payment cards.
Why is PCI Compliance Important?
Trust is the key to your online business. If a security incident occurs, it can wreak havoc on traffic, revenue, and brand reputation. Online shopping is growing in popularity, and eCommerce websites are targets for cyber criminals looking to steal sensitive customer data and credit card information.
How big of a target is your e-commerce website? With automated scripts, hackers can find websites with an online store, scan for vulnerabilities, and gain unauthorized access. Small web stores with few sales aren’t exempt — criminals are opportunists and will target any accessible websites or server resources. It is often easier to hack a thousand small e-commerce websites than it is to hack one large online retailer.
E-commerce websites are susceptible to a number of risks and threats:
- Credit card stealers put your customers at risk of identity theft or credit card fraud.
- Hijacking causes loss of sales when customers are redirected to a fake shopping cart.
- Injected website content can spread spam, malware, and malvertising.
- Server resources can be stolen and used in malware campaigns, DDoS attacks, etc.
- Hacked sites can be blocked by search engines, antivirus programs, and browsers.
- Because there will always be some level of risk, security is a continuous process. A proper e-commerce security strategy requires frequent assessment and diligence.
What Happens If You’re Not PCI Compliant?
If a merchant is found to be non-compliant with the PCI-DSS, there can be a variety of penalties & consequences ranging from fines, loss of time, and reputation damage.
PCI Non-Compliance Fines
Non-PCI compliant websites can suffer hefty penalties by payment industry regulators if customers experience fraudulent transactions. The average cost of a data breach for a small business is $86,500, with enterprise organizations paying 4 million dollars.
GDPR Regulation
Under GDPR, any business that experiences the breach of EU residents’ personal information has 72 hours to notify supervisory authorities or risk facing heavy fines. This regulation joins a number of US federal and state laws which hold organizations accountable for the security of customer data.
Suspension of Credit Cards
Perhaps worse than fines, the ability to accept credit card payments may be revoked. The PCI standards are created by the major credit card companies, and this is their defence against irresponsible merchants. If a data breach occurs for your e-commerce store, the PCI council can revoke the privilege of using their payment cards.
Mandatory Forensic Examination
Merchants suspected of a data breach are required by the PCI-DSS to undergo a mandatory forensic examination, which requires hiring professionals and conducting a time-consuming investigation. A small business examination may cost between $20K to $50K.
Notification and Credit Monitoring
If a compromise of financial information is suspected, a number of states require the merchant to notify customers and inform them of the breach. Merchants may also need to produce up to a year’s worth of credit monitoring or counselling services to affected customers.
Liability for Fraud Charges
Lawsuits may claim liability on merchants for security breaches. It is important to emphasize that protecting your customer’s sensitive information is your responsibility as a business owner. That is why having a secure website is vital.
Credit Card Replacement Costs
Card issuers may require merchants to pay the cost of re-issuing credit cards, which includes shipping, activation, and communication to the customer. These fees can range from $3 to $10 per card.
Reassessment for PCI Compliance
In order for a website to accept credit card transactions again, a complete PCI reassessment by an external Qualified Security Assessor (QSA) must be performed.
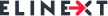
The End Objectives PCI DSS Elaborates On
PCI DSS Objectives
First, The safety of transactions depends on the network security. Firewalls must be robust enough to function without causing any troubles to cardholders. Firewalls are needed for wireless LANs (they are very vulnerable to hacker attacks and eavesdropping). PIN codes (Personal Identification Numbers), passwords and other authentication data should not involve defaults supplied by the vendors. Customers must have an opportunity to change this data as much and as often as they want.
Second, cardholder information is required to have valid protection at the places it is stored. The storage with such data as birth date, mothers maiden names and more important, like Social Security numbers, phone numbers, e-mails must be kept secure. If transmitted via public networks, it should be properly encrypted. Encryption is crucial for any credit cards transaction, including the ones e-commerce websites have to offer.
Third, hacker attacks must be avoided at all costs – the merchant has to use and frequently update anti-virus software and all kinds of anti-malware programs. All the used applications have to be bug-free and do not contain vulnerabilities that enable exploiting of cardholder data (stealing or altering it). Operational systems vendors often offer patches closing these vulnerabilities, so the merchant must ensure they are installed in a proper manner and in time.
Fourth, merchant should close, control and restrict access to the system information. Cardholders must be reassured that their information is needed to effectively carry out a transaction and effectively protected. Every person who uses the computer/system should be assigned an identification alias. The data of cardholders should be protected both physically and electronically
Fifth, networks must be constantly monitored and regularly tested to ensure that all security measures and processes are in place, are functioning properly, and are kept up-to-date. Those anti-virus and anti-spyware programs should be provided with the latest definitions and signatures.
Sixth, a formal information security policy must be defined, maintained, and followed at all times and by all participating entities. Audits and penalties for non-compliance may and be necessary.
PCI DSS Compliance in Elinext
PCI DSS compliance is the requirements that can’t be overlooked if you are processing payments. We as a software development company try to keep a close look at all the requirements for our clients to avoid any troubles with the laws and regulations.
The head of web development at Elinext, Gennady Sergeenko highlighted the fact that some of our customers, potential and existent, often underestimate the value of PCI DSS compliance.
Our business consultants sometimes have to explain the mechanism behind the online payments, the necessity to get all the required licenses and meet all the requirements.
“There are plenty of payment systems out there, take Stripe, for instance. They are pretty easy for us to implement, and there is no need for us a software development company to get any additional certification, nor creating some sort of payment gateway – payment system is PCI DSS compliant”
“We notify our clients about the importance of regulations, promise them full compliance and keep a close look at all the updates in regulations, PCI DSS is not the exception,” – Gennady continues.
There is more to that as our company has experience in development software for fintech startups, and that could require additional expertise, or skill set.
If your project is somehow related with payments, Elinext can assure you, you won’t experience any troubles from “What Happens If You’re Not PCI Compliant?” section.