About Client
The client is a Luxembourg-based financial services company operating in a highly regulated European environment. As part of their regulatory obligations and internal security strategy, the company required centralized security monitoring and incident detection capabilities.
The organization operates a segmented network infrastructure consisting of multiple subnets and server groups. The environment includes Windows-based servers managed through Active Directory, protected by enterprise-grade firewall infrastructure, VPN services, and proxy servers. They are one of our esteemed clients for the financial software development services.
Given the regulatory landscape in Europe and increasing cybersecurity risks, the company needed a Security Information and Event Management (SIEM) development solution capable of collecting, processing, analyzing, and correlating security-related data across the entire infrastructure.
Business Challenge
The client required SIEM implementation services to comply with European information security standards and regulatory requirements.
Although another vendor had initially installed Splunk, the setup was basic and did not fully support advanced security monitoring or automated incident detection, which was to be achieved with SIEM development. The system lacked structured log orchestration, optimized license usage, and well-designed threat detection scenarios.
The key challenges before SIEM development included:
- Designing centralized log ingestion from diverse infrastructure components
- Filtering and structuring logs to optimize Splunk license consumption
- Developing meaningful security correlation scenarios
- Creating automated incident generation mechanisms
- Establishing a scalable foundation for expanding threat coverage
- Delivering results within resource constraints
The client also did not have a dedicated SIEM implementation services specialist, which made independent ownership and architectural decision-making essential.
Process
There is no strict separation between the different parts of custom software development services, but we can more or less mention 6 stages of participation in the process.
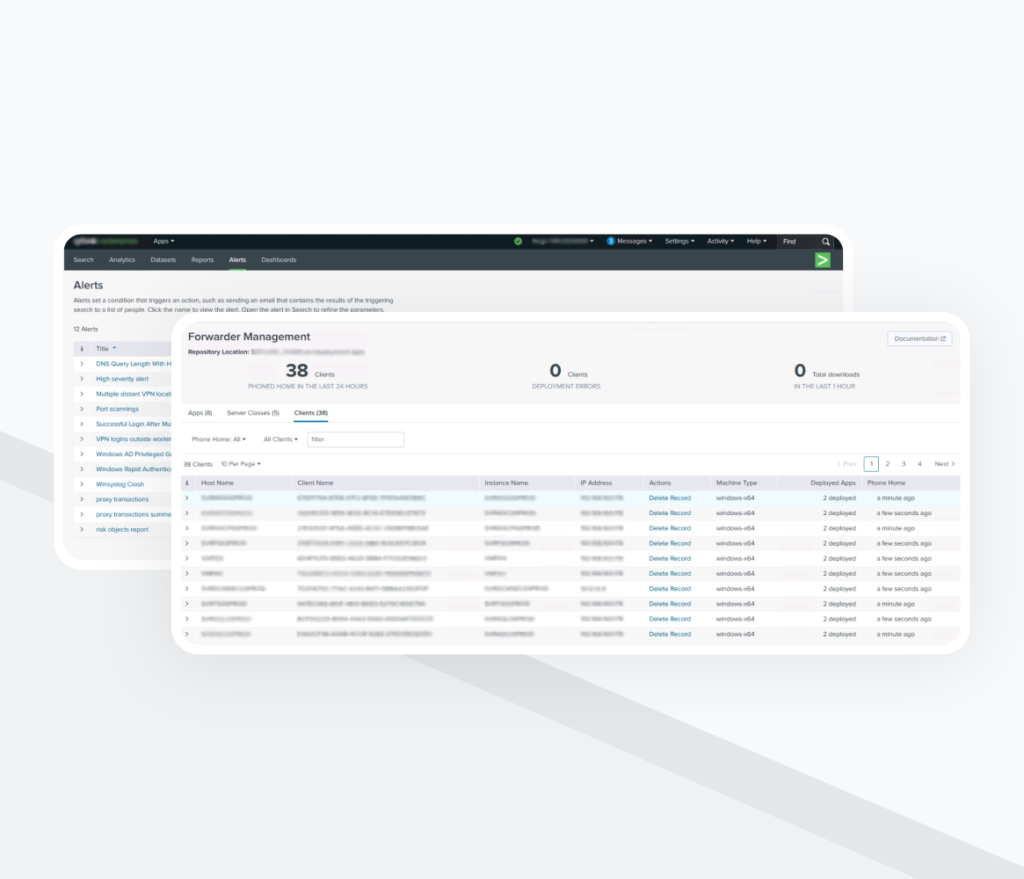
Stage 1: Infrastructure Assessment and License Optimization
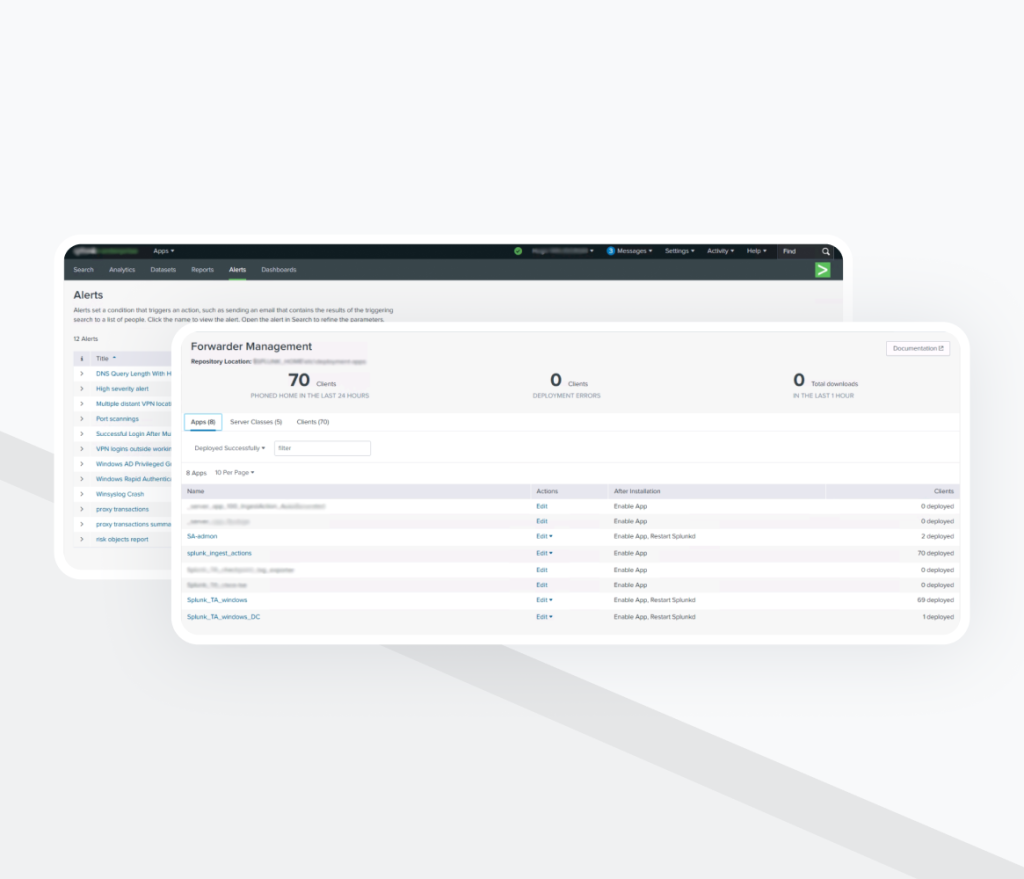
The SIEM implementation services began with a full audit of the existing Splunk environment and infrastructure architecture.
Key activities included:
- Identifying all available log sources
- Analyzing existing forwarder configuration
- Evaluating license consumption
- Reorganizing management to ensure centralized configuration control
A major focus was on determining which log data was truly valuable for security monitoring and which could be filtered out to reduce license usage without compromising visibility.
Stage 2: Log Source Integration and Data Modeling
All available data sources were integrated into the SIEM implementation system:
- Windows Event Logs
- Active Directory events
- DNS logs
- Firewall logs
- VPN logs
- Proxy logs
- OpenPassword account activity
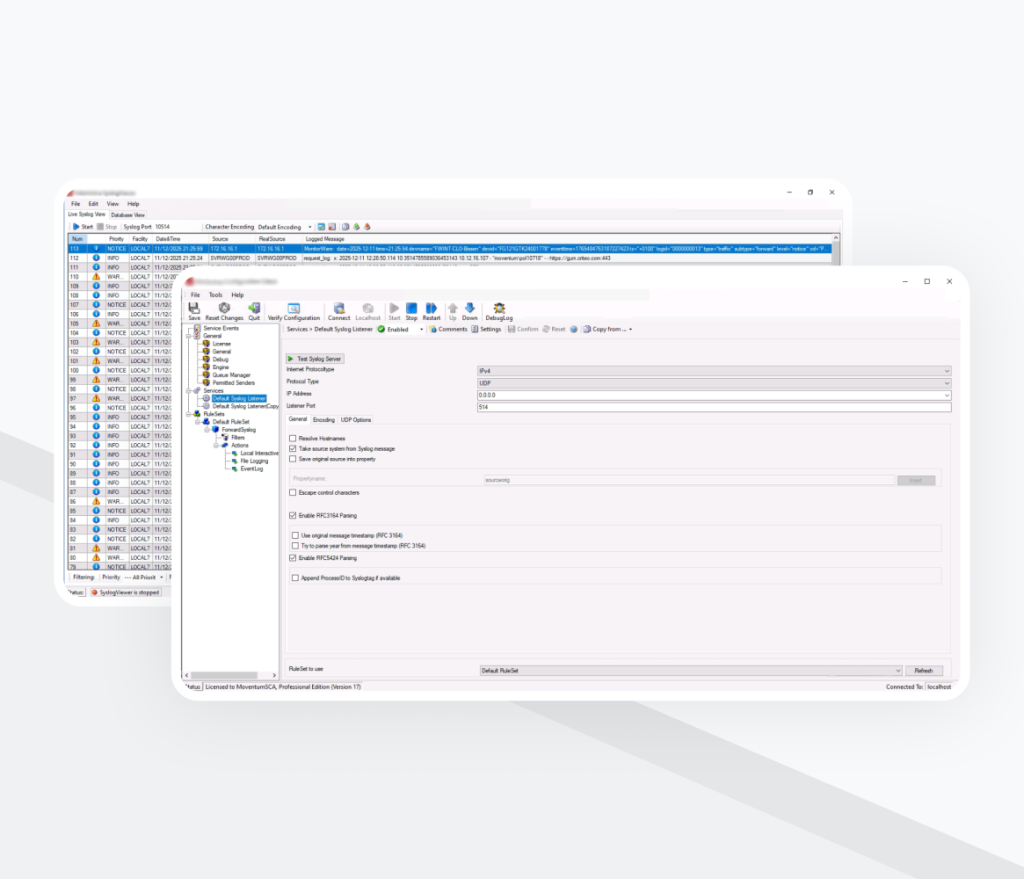
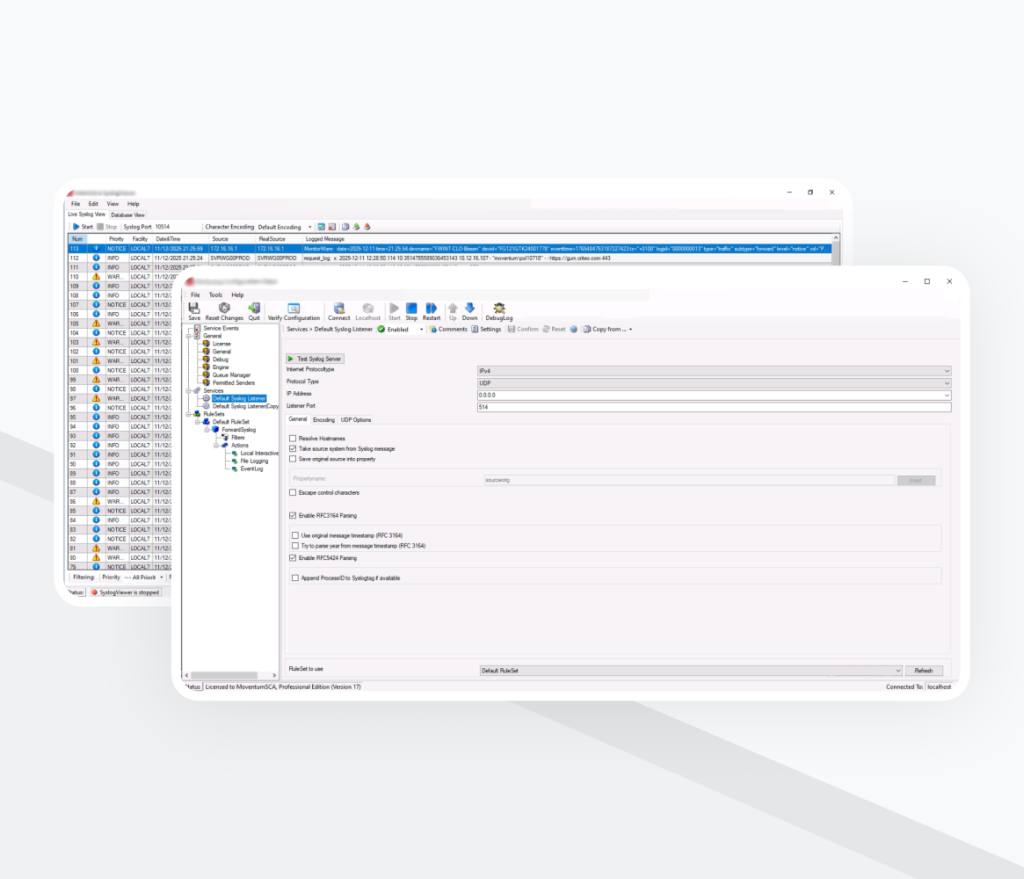
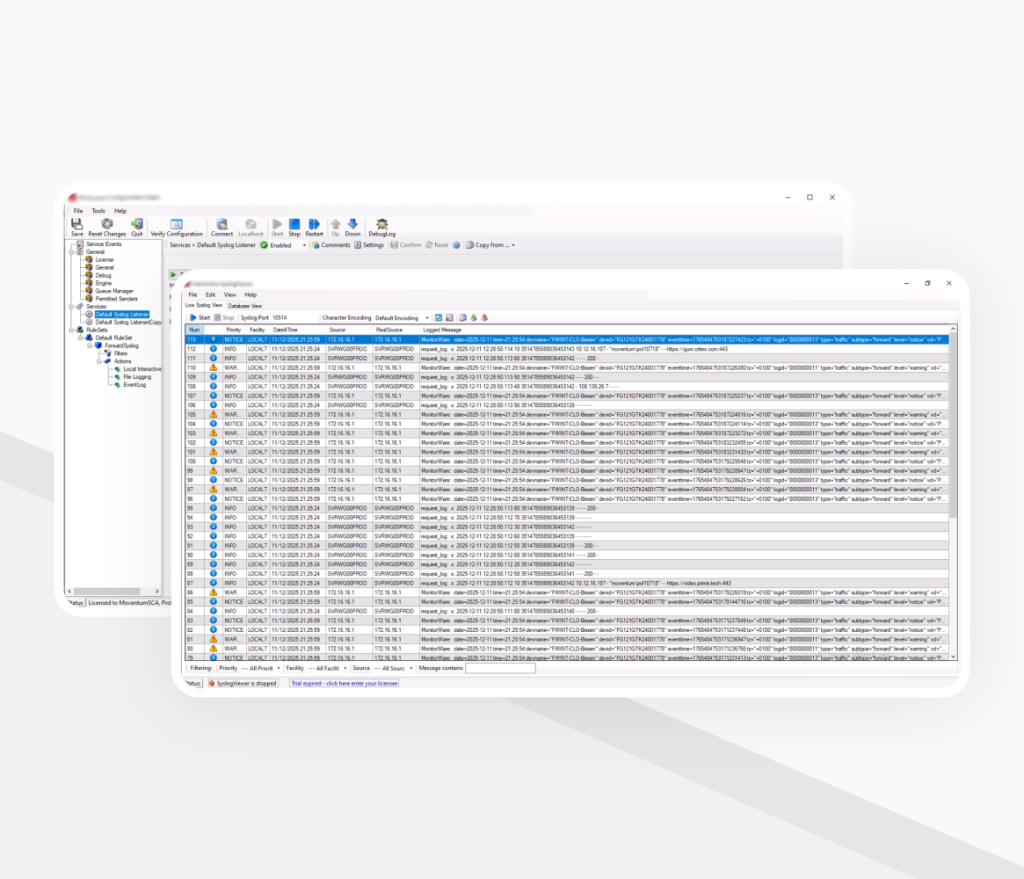
Windows servers sent logs via Splunk forwarders directly to the SIEM server. Firewall, VPN, and proxy logs were delivered to a syslog server, stored as files, and then processed by a forwarder.
During this phase of SIEM development:
- Data was structured into separate indexes
- Field extractions were configured
- Data models were aligned
- Parsing and normalization were optimized
Daily ingestion volume reached 8–10 GB, with total index storage exceeding 300 GB.
Stage 3: Dashboard Development
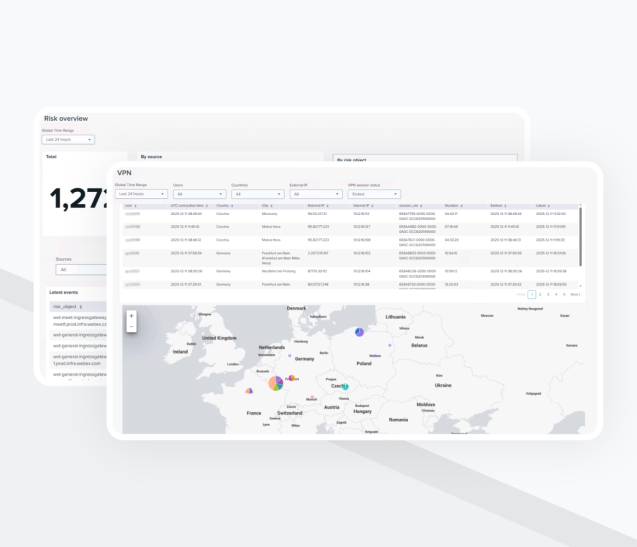
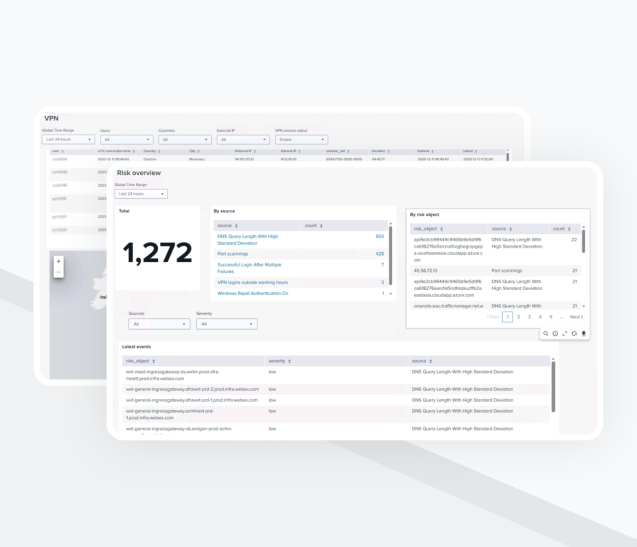
SIEM implementation services included making dashboards. These dashboards were created to provide structured visibility into:
- Network traffic flows
- VPN activity
- Proxy usage
- Firewall events
- Threat detection trends
These dashboards allowed security engineers to quickly navigate data and perform investigations efficiently.
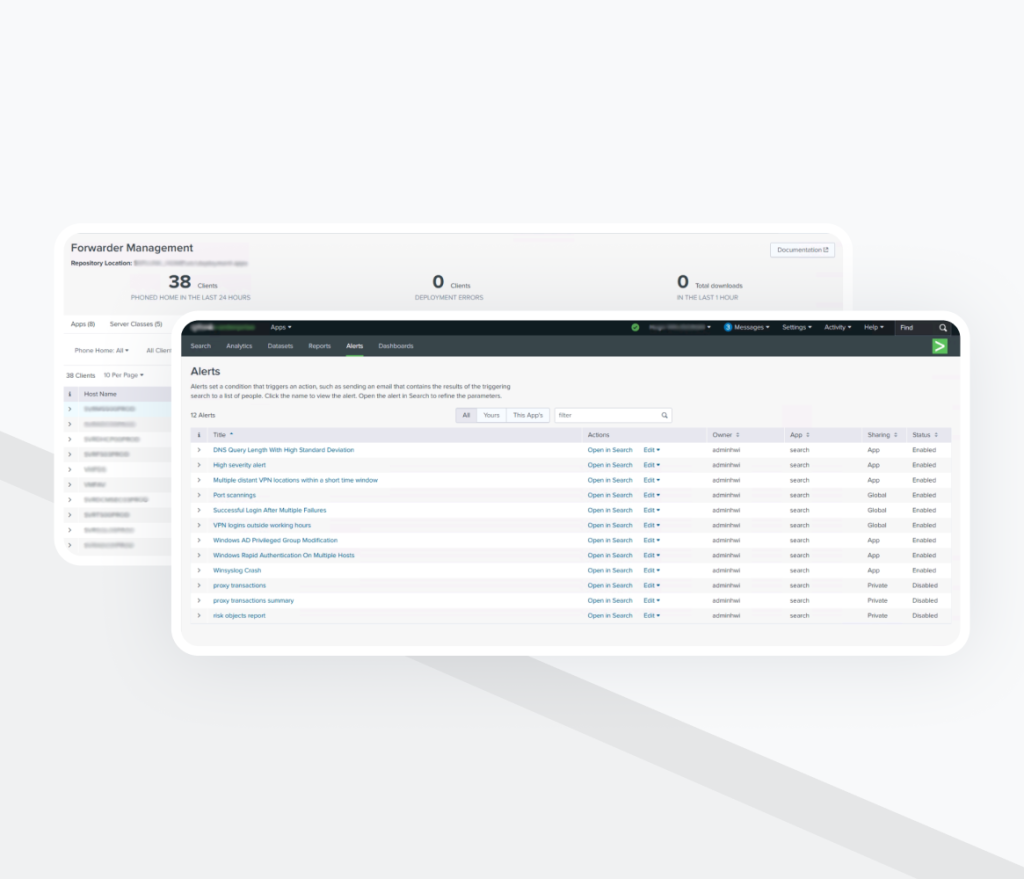
Stage 4: Correlation Search Development
Based on available data sources, relevant security scenarios were identified and designed.
For each scenario:
- Correlation searches were developed
- Threshold logic was defined
- False positives were minimized
Manual testing was conducted using historical data and controlled event triggering
The goal was to ensure automatic incident creation when suspicious activity occurred.
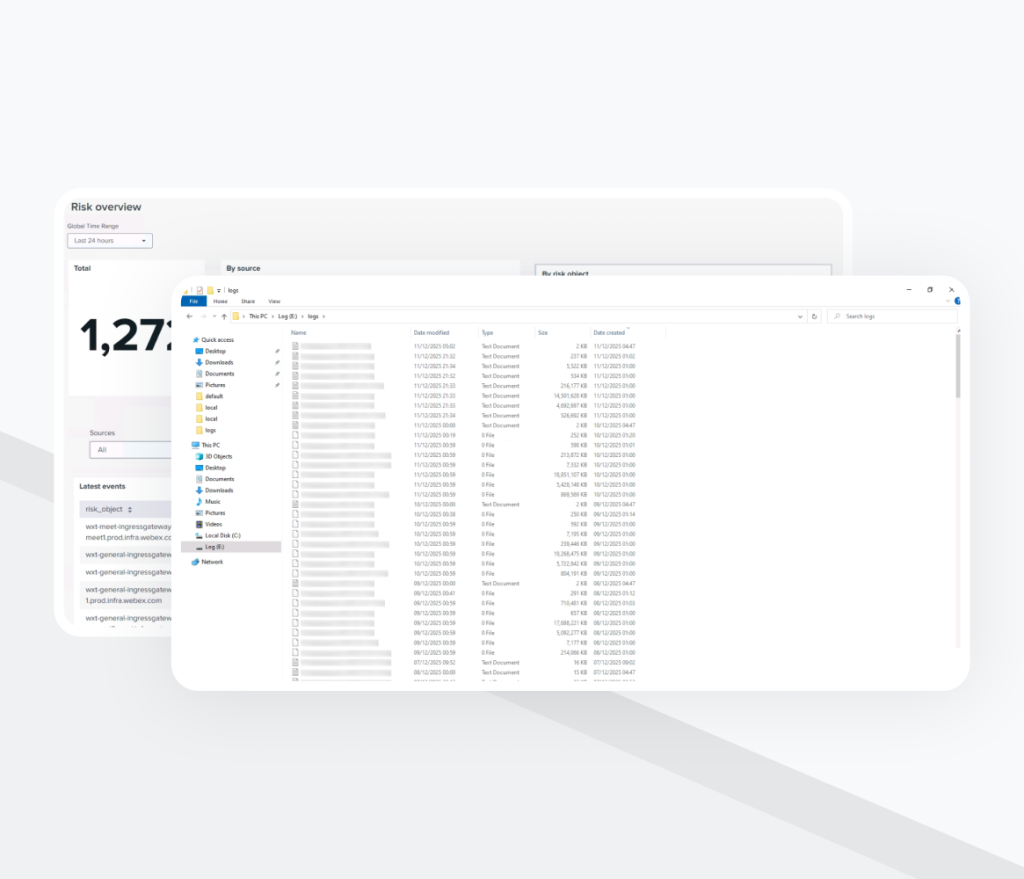
Stage 5: Centralized Incident Index and Alerting
All triggered findings were aggregated into a dedicated correlation index.
This provided:
- A single investigation point
- Structured security incident tracking
- Improved search performance
- Better monitoring visibility
Additionally, during SIEM development, dynamic Jira ticket creation was implemented to automatically generate incidents for security engineers.
Stage 6: Continuous Optimization and Scaling (Ongoing SIEM development)
Due to infrastructure resource constraints, constant optimization was required:
- Iterative query refinement
- Event filtering improvements
- License usage monitoring
- Performance tuning
The system is continuously evolving to expand threat coverage and refine detection quality.
Final Product Overview
The result of our web development services is the solution is a centralized SIEM platform (after QA and software testing services) based on Splunk Enterprise that:
- Collects logs from distributed infrastructure components
- Normalizes and structures security data
- Correlates events across multiple sources
- Automatically generates security incidents
- Integrates with Jira for incident management
- Provides dashboards for operational visibility
The system processes 8–10 GB of security data daily and maintains over 300 GB of indexed historical data.
Business Effects for Client
- Centralized monitoring of 100% of critical infrastructure components (Windows servers, AD, firewall, VPN, proxy, DNS).
- Processing of 8–10 GB of logs daily with over 300 GB of indexed historical data for investigations and audits.
- Automated correlation searches covering key security scenarios (authentication abuse, network anomalies, privileged activity).
- 60–70% reduction in manual incident handling through automatic Jira ticket creation.
- Incident detection improved from manual review (hours) to near real-time alerting (minutes).
- 20–30% optimization of Splunk license usage through log filtering and prioritization.
- Established an auditable monitoring process aligned with European security standards.
- Built a scalable SIEM foundation enabling the gradual expansion of threat detection coverage.